Cyber Security for Business Final Exam Spring 2026
Answer Scripts
We try to add a possible answer here, everyone can contribute in their own way.
No answer scripts have been uploaded for this question yet.
Be the first to upload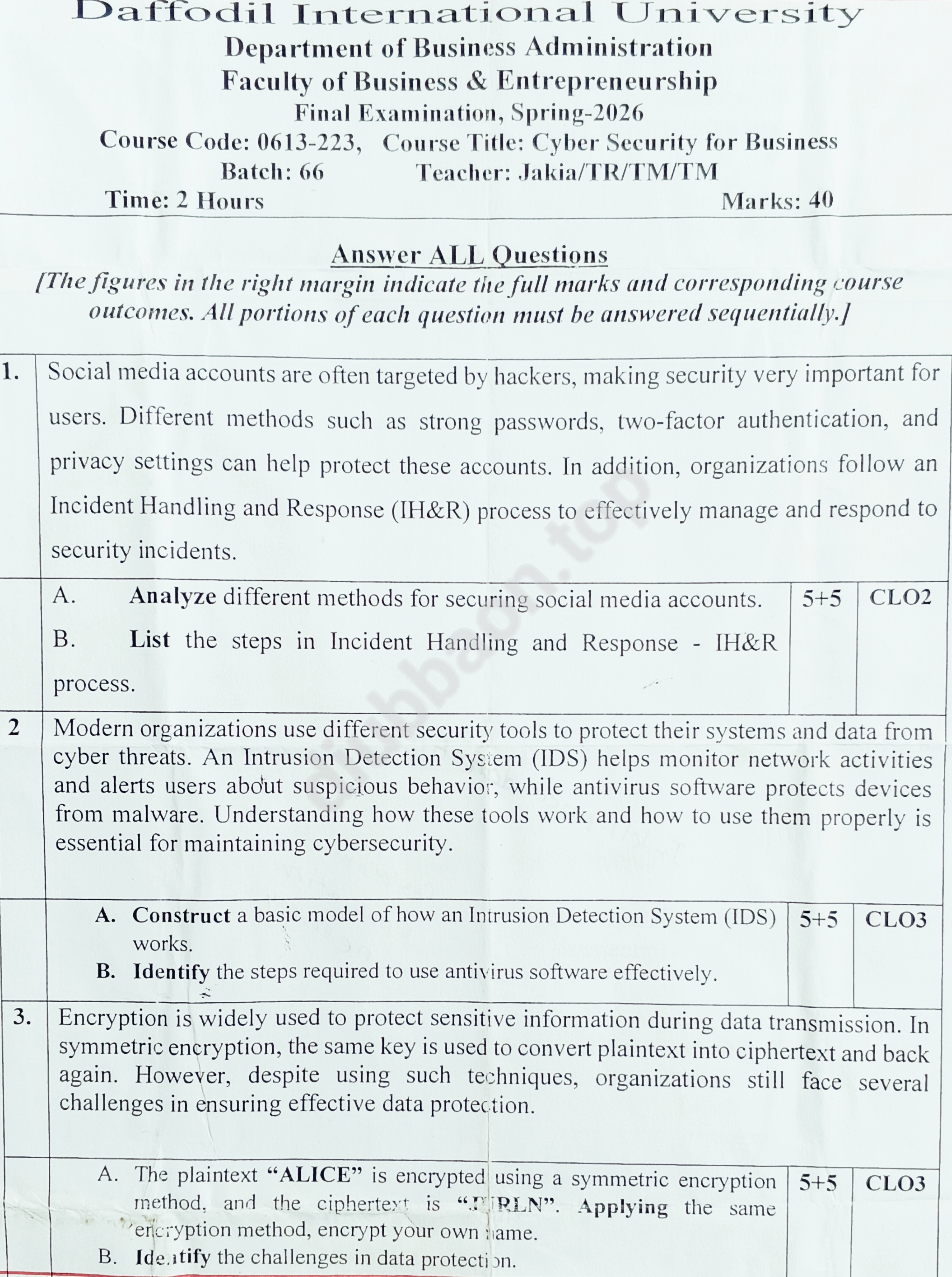
Exam Paper Text Transcript (AI-OCR)
Crawlable past paper text indexed for search optimization.
1. Social media accounts are often targeted by hackers, making security very important for
users. Different methods such as strong passwords, two-factor authentication, and
privacy settings can help protect these accounts. In addition, organizations follow an
Incident Handling and Response (IH&R) process to effectively manage and respond to
security incidents.
A. Analyze different methods for securing social media accounts. 5+5 CLO2
B. List the steps in Incident Handling and Response - IH&R
process.
2 Modern organizations use different security tools to protect their systems and data from
cyber threats. An Intrusion Detection System (IDS) helps monitor network activities
and alerts users about suspicious behavior, while antivirus software protects devices
from malware. Understanding how these tools work and how to use them properly is
essential for maintaining cybersecurity.
A. Construct a basic model of how an Intrusion Detection System (IDS) 5+5 CLO3
works.
B. Identify the steps required to use antivirus software effectively.
3. Encryption is widely used to protect sensitive information during data transmission. In
symmetric encryption, the same key is used to convert plaintext into ciphertext and back
again. However, despite using such techniques, organizations still face several
challenges in ensuring effective data protection.
A. The plaintext “ALICE” is encrypted using a symmetric encryption 5+5 CLO3
method, and the ciphertext is “PLN”. Applying the same
encryption method, encrypt your own name.
B. Identify the challenges in data protection.
How to Use This Paper
Cyber Security for Business Final Exam Spring 2026 is archived for Cyber Security for Business (0613-223) so DIU BBA students can review the actual exam format before sitting for a similar assessment. Use it to identify the marks distribution, repeated chapter areas, and the style of short-answer, analytical, or case-based questions used in Spring-2026 for Batch 66.
A good way to practice is to solve the paper once without notes, mark the questions you could not finish, then compare your answers with class materials or any answer scripts available below. This page also links related papers from the same course area so you can compare question patterns across semesters instead of depending on one file only.
This resource was contributed by Abdur Rahman (241-11-247). If you notice an incorrect course code, semester, batch, or file, contact the archive team so the page can be corrected. If you have a solved version, uploading it helps make this page more complete for the next student.
Frequently Asked Questions
What is the course code for Cyber Security for Business?
The course code for Cyber Security for Business at DIU BBA is 0613-223.
Where can I download Cyber Security for Business Final Exam Spring 2026?
You can download Cyber Security for Business Final Exam Spring 2026 for Cyber Security for Business (0613-223) from the DIU BBA Archive. This question is from the Spring-2026, Batch 66.
Are there answer scripts available for this question?
Currently, no answer script is available for this question. However, if you have one, you can contribute by uploading it to help your fellow students.
Who can access these resources?
These resources are freely available to all students of Daffodil International University. Our goal is to make academic resources easily accessible for everyone.
More from Cyber Security for Business
0613-223 — 9 related questions found